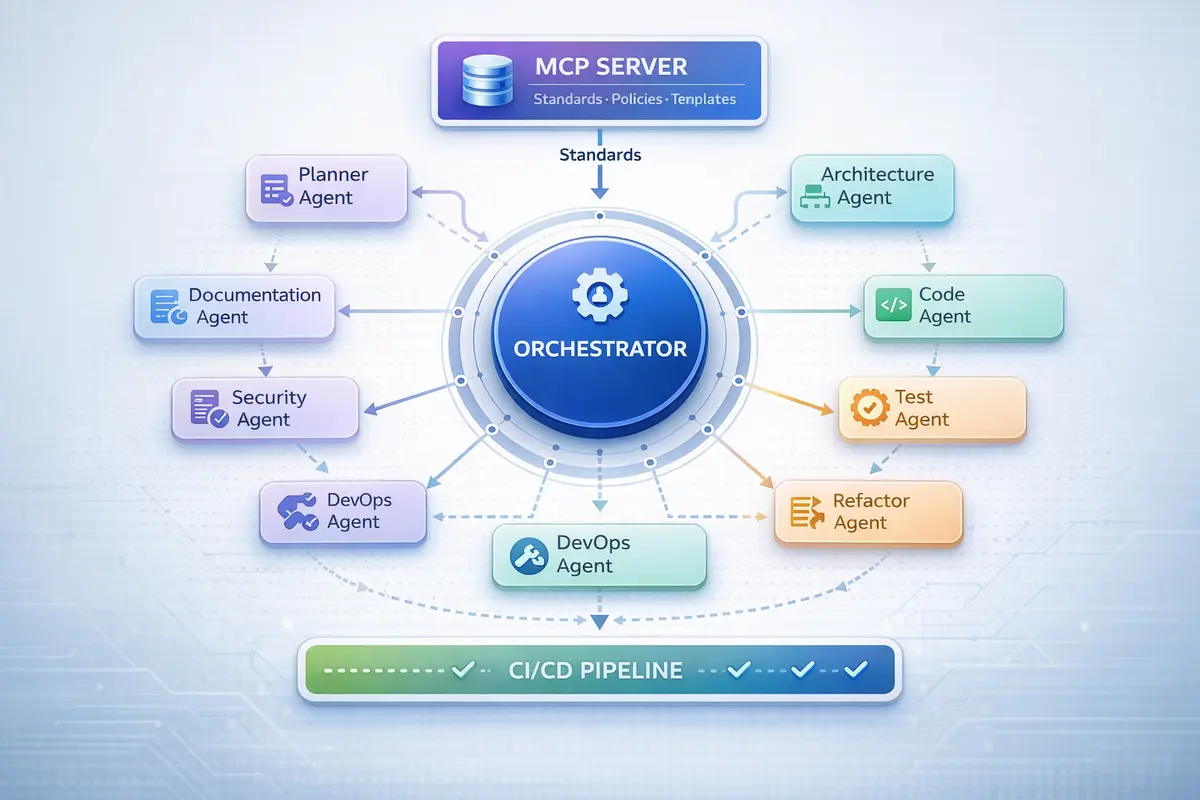
The 2,000-Line Prompt Problem: Building an AI Development Operating System
How a monolithic prompt file evolved into a production AI Development Operating System. Real architecture for multi-agent software development: MCP standards, orchestration patterns, and the phases that actually matter.